The Cisco 300-430 ENWLSI (Implementing Cisco Enterprise Wireless Networks) exam is a key component of the CCNP Enterprise certification. It evaluates your ability to implement wireless solutions, design secure WLANs, and troubleshoot performance issues.
As of November 2025, the 300-430 exam remains active and valid in the CCNP Enterprise certification track, meaning candidates can still pair it with the 350-401 ENCOR exam to earn the full CCNP Enterprise credential.
Updated Exam Format and Key Information
Cisco has refined the 300-430 exam blueprint to align with the latest wireless technologies, including Wi-Fi 6E and automation in enterprise networks.
- Exam Duration: 90 minutes
- Number of Questions: 55–65
- Question Types: Multiple choice, drag-and-drop, simulations, and case-based scenarios
- Passing Score: 750–850/1000 (unofficial estimate)
Main Exam Topics
- Wireless Network Design – WLAN planning, coverage optimization, and roaming strategies.
- FlexConnect and Local Mode – Deployment modes and controller management.
- Quality of Service (QoS) – Traffic prioritization and multicast optimization.
- WLAN Security – WPA3, EAP methods, and integration with Cisco ISE.
- Troubleshooting and Monitoring – Diagnosing performance and connectivity issues.
Why the Cisco 300-430 Exam Matters in 2025
With the increasing adoption of Wi-Fi 6/6E and enterprise IoT networks, wireless engineers remain in high demand.
Professionals certified in ENWLSI often find roles such as Wireless Network Engineer, Network Specialist, or Systems Consultant, with average salaries exceeding $110,000 annually in the U.S. market.
Study Resources for the 300-430 Exam
Effective preparation involves using both official Cisco materials and verified third-party resources.
For candidates who prefer practical learning, Leads4Pass offers a structured question bank and mock exam set that aligns closely with Cisco’s exam topics.
You can review their latest collection of 300-430 PDF and VCE practice tests here:
👉 https://www.leads4pass.com/300-430.html
Cisco Official Updates
Cisco has integrated several key updates into the ENWLSI blueprint:
- Wi-Fi 6E and 7 Technologies: Expanded coverage of 6GHz frequency planning and high-density deployment.
- DNA Center Automation: Greater emphasis on wireless policy automation and network analytics.
- Zero Trust Integration: Stronger focus on authentication, endpoint control, and identity-based access.
Recommended Learning Path for Candidates
- Start with ENCOR (350-401) – Understand enterprise networking fundamentals.
- Transition to ENWLSI (300-430) – Focus on wireless deployment and management.
- Hands-on Labs: Use Cisco Packet Tracer, DNAC Sandbox, or WLC lab environments.
- Practice Tests: Take regular mock exams to measure readiness.
- Join Communities: Participate in the Cisco Learning Network for peer support.
Practical Preparation Tips from Successful Candidates
- Create a weekly study plan: Dedicate 2–3 hours daily for topic review and lab practice.
- Use visual tools: Mind maps and topology diagrams help retain configuration logic.
- Focus on troubleshooting: Learn to interpret logs and identify interference patterns.
- Simulate real networks: Recreate small WLAN environments using virtual controllers or real APs.
Real-World Applications of ENWLSI Knowledge
Candidates who pass the 300-430 often apply their skills in:
- Enterprise Wi-Fi optimization projects
- IoT and sensor network deployment
- Corporate WLAN migration to Wi-Fi 6/6E
- Network automation with DNA Center APIs
These use cases reflect Cisco’s shift toward secure, adaptive wireless infrastructures that support hybrid work and smart buildings.
[Free share] Cisco 300-430 Exam Questions and Answers
| Number of exam questions | Related | Complete material |
| 15 | CCNP | 316 Q&A |
Question 1: Where is a Cisco OEAP enabled on a Cisco Catalyst 9800 Series Wireless Controller?
A. RF Profile
B. Flex Profile
C. Policy Profile
D. AP Join Profile
Correct Answer: B
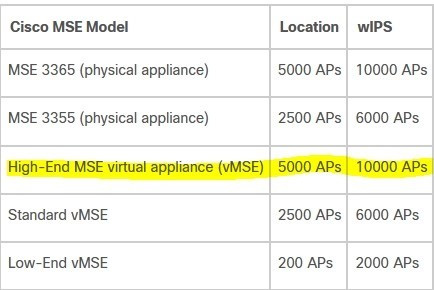
Question 2: Which Cisco vMSE Release 8 option must the engineer deploy?
An engineer configures a deployment to support:
1.
Cisco CMX
2.
licenses for at least 3000 APs
3.
6000 wIPS licenses
The Cisco vMSE appliance must be sized for this deployment.
A. Large vMSE
B. Low-End vMSE
C. Standard vMSE
D. High-End vMSE
Correct Answer: D
Question 3: Which cause of this issue is true?
An engineer configured a Cisco AireOS controller with two TACACS+ servers. The engineer notices that when the primary TACACS+ server fails, the WLC starts using the secondary server as expected, but the WLC does not use the primary
server again until the secondary server fails or the controller is rebooted.
A. Fallback is enabled
B. Fallback is disabled
C. DNS query is disabled
D. DNS query is enabled
Correct Answer: B
Question 4: What is configured to use more than one port on the OEAP to extend the wired network\'s?
A. AAA override
B. client load balancing
C. remote LAN ACL
D. remote LAN
Correct Answer: D
Question 5: Which action ensures that access to the network is restricted for these users unless the correct authentication mechanism is configured?
WPA2 Enterprise with 802.1X is being used for clients to authenticate to a wireless network through a Cisco ISE server. For security reasons, the network engineer wants to ensure that only PEAP authentication is used. The engineer sent instructions to clients on how to configure the supplicants, but the ISE logs still show users authenticating using EAP-FAST.
A. Enable AAA override on the SSID, gather the usernames of these users, and disable the RADIUS accounts until the devices are correctly configured.
B. Enable AAA override on the SSID and configure an ACL on the WLC that allows access to users with IP addresses from a specific subnet.
C. Enable AAA override on the SSID and configure an access policy in Cisco ISE that denies access to the list of MACs that have used EAP-FAST.
D. Enable AAA override on the SSID and configure an access policy in Cisco ISE that allows access only when the EAP authentication method is PEAP.
Correct Answer: D
Question 6:
On a branch office deployment, it has been noted that if the FlexConnect AP is in standalone mode and loses connection to the WLC, all clients are disconnected, and the SSID is no longer advertised. Considering that FlexConnect local switching is enabled, which setting is causing this behavior?
A. ISE NAC is enabled
B. 802.11r Fast Transition is enabled
C. Client Exclusion is enabled
D. FlexConnect Local Auth is disabled
Correct Answer: D
Question 7: Which customizable security report on Cisco Prime Infrastructure will show rogue APs detected since a point in time?
A. Network Summary
B. Rogue APs Events
C. New Rogue APs
D. Rogue APs Count Summary
Correct Answer: C
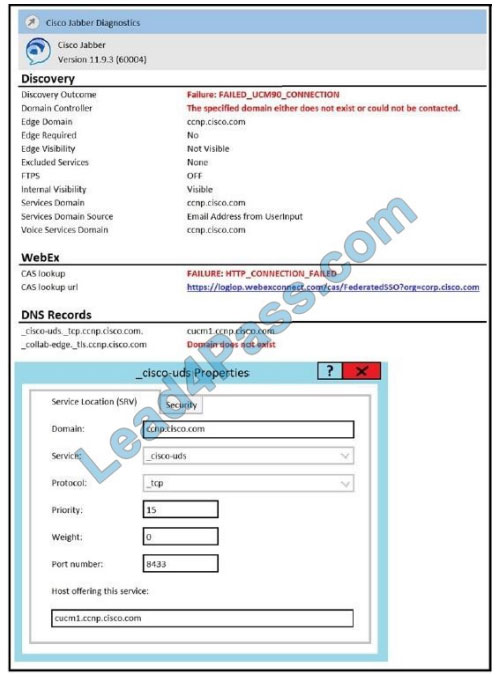
Question 8: Which marking value must be trusted on port Fa 0/6?
Refer to the exhibit.
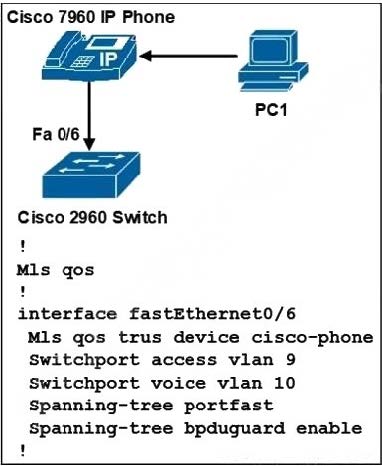
An engineer must preserve a QoS marking sent by the Cisco Jabber software running on PC1.
A. DSCP
B. 802.1p
C. CoS
D. IP precedence
Correct Answer: A
Question 9: How does the engineer accomplish this task without using Cisco ISE?
ALLAR A network engineer must segregate all iPads on the guest WLAN to a separate VLAN.
A. Enable RADIUS DHCP profiling on the WLAN.
B. Create a local policy on the WLC.
C. Use an mDNS profile for the iPad device.
D. Use 802.1x authentication to profile the devices
Correct Answer: B
Question 10: Which option is an impact of BYOD should be considered?
A company wants to switch to BYOD to reduce IT support costs for the company.
A. increased VPN connections
B. restricted device enforcement
C. increased phishing attacks
D. decreased support calls
Correct Answer: A
Question 11: How should the CAPWAP multicast group address be assigned during configuration?
An engineer is configuring multicast for two WLCs. The controllers are in deferent physical locations and each handles around 500 wire clients.
A. Each WLC must be assigned a unique multicast group address
B. Each WLC management address must be in the same multicast group
C. Each WLC management address must be in a different multicast group
D. Both WLCs must be assigned the same multicast group address
Correct Answer: A
Question 12: Which two configurations on the wired network ensure end-to-end QoS?
An engineer set up a VoWLAN with QoS on the WLC and a class map on the switch, but the markings are not being preserved correctly in the end-to- end traffic flow. (Choose two.)
A. trust boundaries
B. access lists
C. policy maps
D. QoS licenses
E. NetFlow
Correct Answer: BC
Question 13: Which controller mapping must be modified for this feature?
A network engineer is configuring a Cisco FlexConnect AP to allow Cisco ISE to dynamically assign the subnet of a user based on their credentials.
A. WLAN VLAN
B. VLAN ACL
C. RF group
D. AP group
Correct Answer: D
The AP group configuration includes various parameters that define the behavior and settings of the access points within the group. By modifying the AP group, the network engineer can configure the FlexConnect APs to communicate with Cisco ISE for dynamic VLAN assignment based on user credentials.
Question 14: What is the cause of the problem?
Refer to the exhibit.
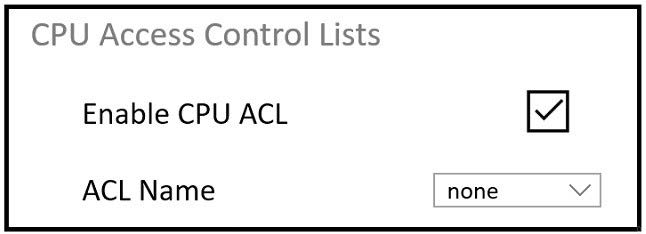
An engineer must restrict some subnets to have access to the WLC. When the CPU ACL function is enabled, no ACLs in the drop-down list are seen.
A. The ACL does not have a rule that is specified to the Management interface.
B. No ACLs have been created under the Access Control List tab.
C. When the ACL is created, it must be specified that it is a CPU ACL.
D. This configuration must be performed through the CLI and not though the web GUI.
Correct Answer: B
Question 15:
When using a Cisco Catalyst 9800 Series Wireless Controller, which statement about AutoQoS is true?
A. It has a set of predefined profiles that you cannot modify further
B. It matches traffic and assigns each matched packet to QoS groups
C. It automates deployment of wired QoS and makes wireless QoS implementation easier
D. It allows the output policy map to put specific QoS queues into specific subgroups
Correct Answer: B
...
Exam Strategy and Time Management
- Understand the question pattern: Identify keywords quickly.
- Flag uncertain questions: Revisit them after completing the easier ones.
- Avoid overthinking simulation tasks: Focus on logical steps, not guesswork.
- Review wireless fundamentals: Don’t skip RF basics, even if you’re experienced.
Maintaining Motivation During Study
It’s easy to feel overwhelmed by the technical depth of ENWLSI. Try:
- Breaking topics into daily “micro goals.”
- Studying with peers online.
- Rewarding yourself after completing each section.
Consistency matters more than long, irregular study sessions.
Post-Exam Career Path
After passing 300-430, you can:
- Advance to CCNP Enterprise certification (with ENCOR).
- Explore roles in wireless design, mobility, and security.
- Prepare for higher-level certifications like CCIE Enterprise Wireless.
Ethical Use of Dumps and Practice Resources
Always use dumps as practice references, not as shortcuts.
Authentic study ensures better understanding, stronger performance, and long-term value for your career.
Platforms like Leads4Pass provide legitimate and verified study materials — not exam leaks — aligned with Cisco’s published topics.
Final Thoughts
The Cisco 300-430 ENWLSI exam remains one of the most relevant wireless certifications for enterprise professionals in 2025.
By combining official study guides, hands-on labs, and trusted practice tests, candidates can confidently master the skills needed to design, implement, and troubleshoot advanced wireless networks.
If you’re preparing now, consider reviewing the updated resources available at:
👉 https://www.leads4pass.com/300-430.html
Thanks for reading — and best of luck on your certification journey!
FAQs
Q1: Is the Cisco 300-430 exam still valid in 2025?
Yes, it remains an active specialization under the CCNP Enterprise certification.
Q2: What’s the average preparation time?
Most candidates need 4–6 weeks of consistent study and lab practice.
Q3: Does the exam include Wi-Fi 6E questions?
Yes, the 2025 version covers Wi-Fi 6E planning and configuration.
Q4: Can I use Packet Tracer for wireless practice?
Yes, though real or simulated WLC environments provide better realism.
Q5: Where can I find reliable 300-430 study material?
Official Cisco Learning Network and verified platforms like Leads4Pass provide structured resources.