Easily get the latest Cisco CCNA Security 210-260 dumps, "Implementing Cisco Network Security (IINS)" 210-260 Exam. You can upgrade your skills by downloading the 210-260 pdf or the online 210-260 exam exercise test! 99.5% pass rate:leads4pass.com
Table of Contents:
- Latest Nicky Cisco CCNA Security 210-260 pdf
- Latest Cisco CCNA Security 210-260 Practice Questions and Answers
- Latest Cisco CCNA Security 210-260 YouTube videos:
- Related 210-260 Popular Exam resources
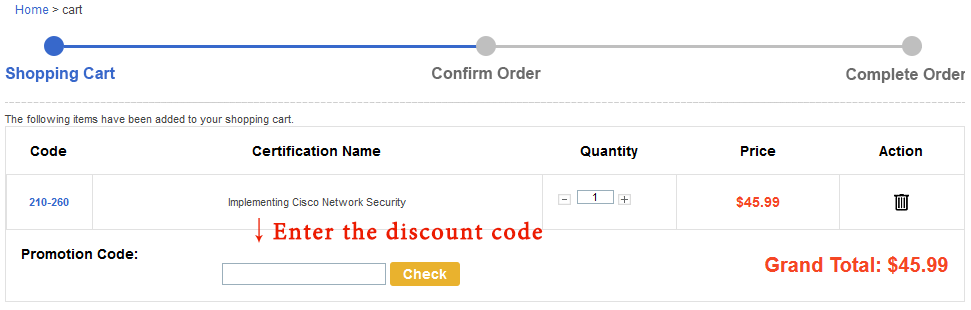
- leads4pass Promo Code 12% Off
- Why Choose leads4pass?
Latest Nicky Cisco CCNA Security 210-260 pdf
[PDF] Free Cisco CCNA Security 210-260 pdf dumps download from Google Drive: https://drive.google.com/open?id=18g6SvjFACTYNFLSKSTyQQ9v_tk78GEnN
[PDF] Free Full Cisco pdf dumps download from Google Drive: https://drive.google.com/open?id=1CMo2G21nPLf7ZmI-3_hBpr4GDKRQWrGx
210-260 IINS - Cisco: https://www.cisco.com/c/en/us/training-events/training-certifications/exams/current-list/iins-210-260.html
Latest Cisco CCNA Security 210-260 Practice Questions and Answers
QUESTION 1
How does a zone pair handle traffic if the policy definition of the zone pair is missing?
A. It permits all traffic without logging.
B. It drops all traffic.
C. It inspects all traffic.
D. It permits and logs all traffic.
Correct Answer: B
QUESTION 2
What is a reason for an organization to deploy a personal firewall?
A. To protect endpoints such as desktops from malicious activity.
B. To protect one virtual network segment from another.
C. To determine whether a host meets minimum security posture requirements.
D. To create a separate, non-persistent virtual environment that can be destroyed after a session.
E. To protect the network from DoS and syn-flood attacks.
Correct Answer: A
The term personal firewall typically applies to the basic software that can control Layer 3 and Layer 4 access to client
machines. HIPS provides several features that offer more robust security than a traditional personal firewall, such as
host intrusion prevention and protection against spyware, viruses, worms, Trojans, and other types of malware. Source:
Cisco Official Certification Guide, Personal Firewalls and Host Intrusion Prevention Systems, p.499
QUESTION 3
In which three ways does the RADIUS protocol differ from TACACS? (Choose three.)
A. RADIUS uses UDP to communicate with the NAS.
B. RADIUS encrypts only the password field in an authentication packet.
C. RADIUS authenticates and authorizes simultaneously, causing fewer packets to be transmitted.
D. RADIUS uses TCP to communicate with the NAS.
E. RADIUS can encrypt the entire packet that is sent to the NAS.
F. RADIUS supports per-command authorization.
Correct Answer: ABC
QUESTION 4
Which protocol offers data integrity, encryption, authentication, and antireplay functions for IPsec VPN?
A. AH protocol
B. ESP protocol
C. IKEv2 protocol
D. IKEv1 protocol
Correct Answer: B
IP Security Protocol—Encapsulating Security Payload (ESP)
Encapsulating Security Payload (ESP) is a security protocol used to provide confidentiality (encryption), data origin
authentication, integrity, optional antireplay service, and limited traffic flow confidentiality by defeating traffic flow
analysis.
http://www.ciscopress.com/articles/article.asp?p=24833andamp;seqNum=3
QUESTION 5
Which ports need to be active for AAA server to integrate with Microsoft AD
A. 445 and 8080
B. 443 and 389
C. 445 and 389
D. 443 and 8080
Correct Answer: C
QUESTION 6
What VPN feature allows Internet traffic and local LAN/WAN traffic to use the same network connection?
A. split tunneling
B. hairpinning
C. tunnel mode
D. transparent mode
Correct Answer: A
Split tunneling is a computer networking concept which allows a mobile user to access dissimilar security domains like a
public network (e.g., the Internet) and a local LAN or WAN at the same time, using the same or different network
connections. This connection state is usually facilitated through the simultaneous use of, a Local Area Network (LAN)
Network Interface Card (NIC), radio NIC, Wireless Local Area Network (WLAN) NIC, and VPN client software
application without the benefit of access control. Source: https://en.wikipedia.org/wiki/Split_tunneling
QUESTION 7
You are configuring a NAT rule on a Cisco ASA. Which description of a mapped interface is true?
A. It is mandatory for all firewall modes.
B. It is mandatory for identity NAT only.
C. It is optional in transparent mode.
D. It is optional in routed mode.
Correct Answer: D
QUESTION 8
Which is a key security component of MDM deployment?
A. Using the network-specific installer package
B. Using self-signed certificates to validate the server – generate a self-signed certificate to connect to the server (Deployed
certificates; Issued certificate to the server likely)
C. Using application tunnel
D. Using MS-CHAPv2 as primary EAP method
Correct Answer: B
QUESTION 9
When is the best time to perform an anti-virus signature update?
A. Every time a new update is available.
B. When the local scanner has detected a new virus.
C. When a new virus is discovered in the wild.
D. When the system detects a browser hook.
Correct Answer: A
QUESTION 10
Which option is the most effective placement of an IPS device within the infrastructure?
A. Inline, behind the internet router and firewall
B. Inline, before the internet router and firewall
C. Promiscuously, after the Internet router and before the firewall
D. Promiscuously, before the Internet router and the firewall
Correct Answer: A
Firewalls are generally designed to be on the network perimeter and can handle dropping a lot of the non- legitimate
traffic (attacks, scans, etc.) very quickly at the ingress interface, often in hardware. An IDS/IPS are, generally speaking,
doing more deep packet inspections and that is a much more computationally expensive undertaking. For that reason,
we prefer to filter what gets to it with the firewall line of defense before engaging the IDS/IPS to analyze the traffic flow.
Source: https://supportforums.cisco.com/discussion/12428821/correct-placement-idsips- network-architecture
QUESTION 11
Which EAP method uses Protected Access Credentials?
A. EAP-FAST
B. EAP-TLS
C. EAP-PEAP
D. EAP-GTC
Correct Answer: A
Flexible Authentication via Secure Tunneling (EAP-FAST) is a protocol proposal by Cisco Systems as a replacement for
LEAP. The protocol was designed to address the weaknesses of LEAP while preserving the "lightweight"
implementation. Use of server certificates is optional in EAP-FAST. EAP-FAST uses a Protected Access Credential
(PAC) to establish a TLS tunnel in which client credentials are verified. Source: https://en.wikipedia.org/wiki/Extensible_Authentication_Protocol
QUESTION 12
What are the primary attack methods of VLAN hopping? (Choose two.)
A. VoIP hopping
B. Switch spoofing
C. CAM-table overflow
D. Double tagging
Correct Answer: BD
QUESTION 13
Which command do you enter to enable authentication for OSPF on an interface?
A. router(config-if)#ip ospf message-digest-key 1 md5 CISCOPASS
B. router(config-router)#area 0 authentication message-digest
C. router(config-router)#ip ospf authentication-key CISCOPASS
D. router(config-if)#ip ospf authentication message-digest
Correct Answer: D
All of our exam dumps are updated throughout the year, follow us! Get the latest recommendations! Pass the Cisco CCNA Security 210-260 exam We recommend: https://www.leads4pass.com/210-260.html (505 Q&A).
Related 210-260 Popular Exam resources
| title | youtube | 210-260 IINS - Cisco | leads4pass | leads4pass Total Questions | |
|---|---|---|---|---|---|
| Cisco 210-260 | leads4pass 210-260 dumps pdf | leads4pass 210-260 youtube | 210-260 IINS - Cisco | https://www.leads4pass.com/210-260.html | 505 Q&A |
| Cisco CCNA Security | https://www.leads4pass.com/640-554.html | 308 Q&A |
leads4pass Promo Code 12% Off
Why Choose leads4pass?
leads4pass helps you pass the exam easily! We compare data from all websites in the network, other sites are expensive,
and the data is not up to date, leads4pass updates data throughout the year. The pass rate of the exam is above 98.9%.